This message kind of follows on from the post about my Fiancée’s hotmail account being compromised, and her subsequent use of much better passwords.
About a week ago I got a message from my brother telling me that my windows live messenger account was spamming him. This was confirmed a little later by another friend but as I was travelling in Germany at the time for work, I was not able to log on and try to change my password immediately. When I was able to sit down with my laptop and internet access, I was pleased to find that I could still log in to windows live and I promptly changed my password.
This compromise was a bit of a surprise and lead me to think about how my account could get compromised, and what I lessons I could learn from the compromise. This post is about how I think my account was compromised, and how I have further strengthened my security since.
While my windows live password was fairly secure (it didn’t conform to any of the common patterns used for passwords) and it wasn’t overly short. Because of this, I’m pretty confident that a brute force attack over the internet against the windows live authentication services would take too much time to make it a reasonable attack vector; it would be prohibitively slow. I would also expect the windows live authentication services to have some kind of security measure to counter brute force attacks, though I’m not sure about that.
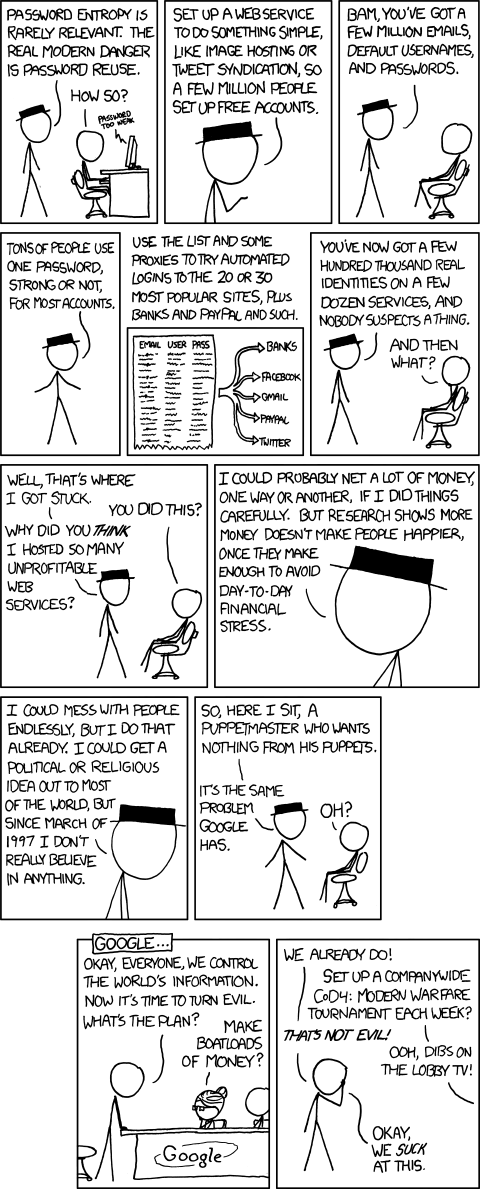
When I set up my windows live account many years ago, I wasn’t really bothered about security and I used the same password for many of my online accounts. There is another great xkcd comic about this: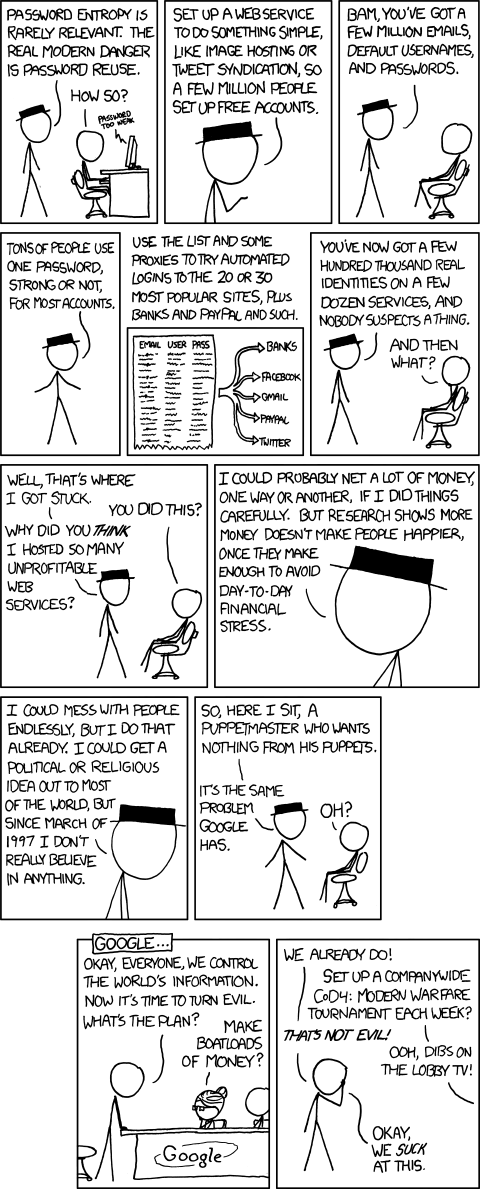
When I realised that this was insecure I started to change some of my accounts to use a slightly different password where a small number of characters were different. The changed characters were chose depending on which site or service I was logging in to, but I had never updated the password on my windows live account because I never logged in manually; I had windows live messenger set to save my password and log in automatically. This meant that I was still probably reusing a password with another account somewhere else that I had forgotten about.
My theory of how they got my password is that a website or service that I had forgotten about (because I haven’t used it for years) has been compromised and had revealed my email address and password. The password was probably stored (and therefore revealed) as plain text. I think this because even if my password was hashed but not unsalted, the attacker would have had to use a very large rainbow table for it to cover my password, and this would have also taken so much time that it would not have been worth it for the attacker. The attacker would surely just go for the low hanging fruit, rather than spend ages on a single account. I think that once the attackers got the email/password combination, they probably just tried it on a bunch of common services that they could use to send spam messages (hotmail, facebook, twitter, skype, WLM, iCloud, etc), and found that one of my accounts had the same password.
I use lastpass these days, with two factor authentication using google authenticator app on my phone, and have been going through my various accounts, making sure they are using unique and secure passwords (the lastpass security challenge is great for this – I am now up to 92.6% secure) but as I mentioned before, I hadn’t logged in to windows live manually for years, so my vault didn’t contain that password, and so couldn’t warn me that I was still reusing a password. So I have racked by brain to try to remember anywhere else that I may have an account and made sure that I checked those passwords too. I’m sure I will have missed some, but hopefully they are ones that I don’t really care about or use these days.